
Redirect local ports with firewalld
Redirecting local ports with iptables directly isn’t too difficult, but can we use firewalld to get the same result? 🧱

Redirecting local ports with iptables directly isn’t too difficult, but can we use firewalld to get the same result? 🧱

Podman’s new quadlet feature lets you specify container launch configuration via simple systemd-like unit files. 📦

1Password has a handy quick access launcher and you can bring it on screen for fast access to passwords and two factor codes in Sway. 🔐

New experiences bring joy! After working with fun AWS CloudFront hacks at work this week, I decided to migrate this blog to AWS S3 and CloudFront. ⛅

Watchtower keeps an eye on your running containers and updates them when new containers appear upstream. 📦
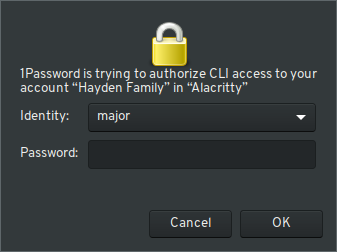
1Password’s CLI tool connects via PolicyKit to the 1Password application for authentication, but this isn’t the easiest in i3. 🔑
Add encrypted ssh keys to your workflow more efficiently with gnome-keyring in the sway window manager.
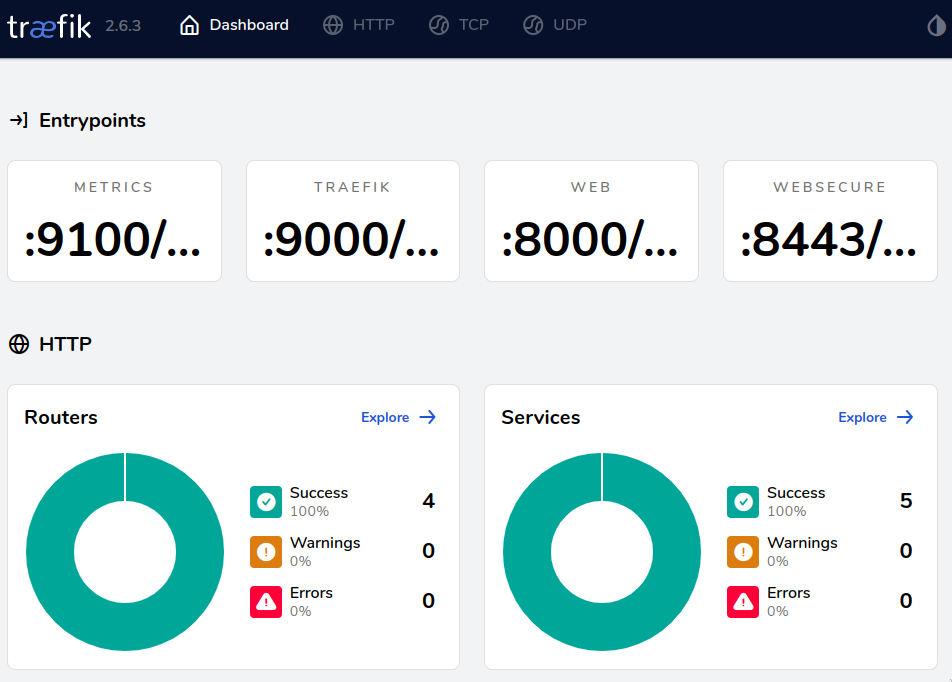
Keep prying eyes away from your sites behind Traefik with basic authentication. 🛃
Store encrypted kubernetes secrets safely in your gitops repository with easy-to-use age encryption. 🔐

Tailscale provides a handy private network mesh across multiple devices but it needs security just like any other network. 🕵

Learn how to forward ports with firewalld for IPv4 and IPv6 destinations. 🕵🏻

...

...
...
...
Environment variables are easy to add to OpenShift deployments, but a more secure way to add these variables is by referencing a secret.

...

...
...

...
...
...
...
...

...

...
...
...
...

...

...

...
...
...
...
...
...
...
...
...
...
...
...
...
Libvirt is a handy way to manage containers and virtual machines on various systems. On most distributions, you can only access the libvirt daemon via the root user by default. I’d rather use a regular non-root user to access libvirt and limit that access via groups. ...
...
...
...
...
...